A Bizarre New Malware Targeting Mac Computers Via Google Search Results

Recently, a new malware threat has been uncovered that attacks Mac users via the Google Search results. The malicious software avoids detection by macOS Catalina security engines.
As stated in the latest report by Intego, this bizarre malware, an advanced variant of the Shlayer trojan, was discovered by security researchers when running searches on Google. The report also states that this malicious software is easily accessible when searching for specific YouTube videos using Google’s search results pages.
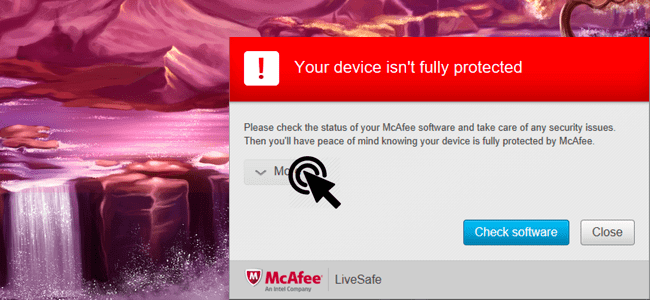
According to the study, Apple's inbuilt protection measures are bypassed by malicious software developers by using Google search results to attack users. Such an approach goes undetected by most virus scanning tools and applications. One of the most common ways to deploy malware is by using Flash player update prompts.
Adobe has confirmed that Flash player is losing relevance. It’ll stop updating the program in 2020. It has also been stated that the feature is scarcely used in web design these days, forcing most browsers to uninstall it.
However, security researchers say that most people believe that they need Flash Player because it has been such an important part of the Internet for so long.
To infect even more computers, malicious software developers prey on people's need for the program, sometimes disguising dangerous files as Flash updates.
How It Works
This newly found malware has been circulating on Google and can bypass the built-in security of macOS devices. The payload of this malware unleashes deceptive pop-ups that are ridden with tricky installer files.
Most of the corrupted files are found when a user searches for specific YouTube videos through the Google search engine.
Once the user searches the video, several non-YouTube links appear in the search results page. When you click on these, it’ll redirect the user multiple times to fake landing pages.
These landing pages claim that the device’s Adobe Flash is outdated. The pop-ups are detailed, realistic, and mimic the original pop-ups, thus tricking unsuspecting users into downloading the malicious file.
Once downloaded and executed, the malware opens a terminal window and runs some code before disappearing. To prove its legitimacy, it’ll even open an actual Flash player installation file and update the program. Afterward, your device starts performing slowly and will be piled with PUPs and ads whenever the user accesses any web browser.
What Can You Do About It?
The secret behind this malware is its deceptive instructions. When you receive a pop-up to update your Flash player and download the file, the guide tells you to right-click the file to open it. When you do so, it bypasses Mac’s inbuilt security that only allows Apple-signed apps/programs to install. Once installed, this program erases its default icon and hides all of its traces.
You can protect yourself by being aware. If you receive any such pop-ups asking for a Flash player update, don’t click it. Instead, visit Adobe’s official website to verify if an update is necessary. Even if an update is necessary, don’t download it from any source except the official website.
Additionally, install a Mac-centric antivirus product that relies on behavioral analysis and heuristic monitoring to add extra layers of security to your device.
Bottom Line
Malware targeting macOS is on the rise. It’s important to stay alert and follow safe browsing habits. Don’t click on random ads and pop-ups.
If you need to update software, do it through the official website and not through third-party websites. Most importantly, use a Mac-centric antivirus for additional security.