What is Email Spoofing?
Email spoofing is a type of cyber attack where the hacker forges an email's sender address. Essentially, a spoofed email will appear to come from a source you know and trust but was actually sent by a nefarious individual.
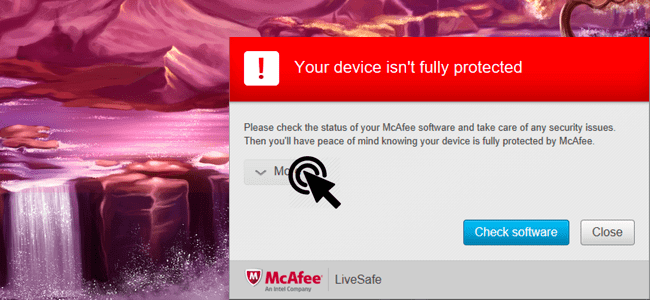
The goal of email spoofing is to trick you into taking action, although this action will always be to your detriment. For example, the bad actor might impersonate a well-known brand, encourage you to click a malicious link, open a malware attachment, or share sensitive information like your login credentials or banking details.
Beyond the 'From' address, spoofed emails typically look very legitimate as a whole, even copying the branding, logos, and language used by the trusted entity.
How Email Spoofing Works
Email spoofing works because the Simple Mail Transfer Protocol (SMTP) doesn't authenticate email addresses on its own. Therefore, it's fairly easy for a bad actor to change the metadata of an email to impersonate a different sender. They simply manipulate the 'From,' 'Reply-To,' and 'Return Path' fields so that everything looks above board.
There are different types of email spoofing. For instance, if an email address is identical to the trusted one, this is known as domain spoofing. However, domain spoofing isn't always possible, and cyber criminals instead rely on domain-lookalike spoofing. This is where the email address looks almost identical but uses substitute characters, e.g., customerservice@Amaz0n.com. Unfortunately, people only tend to notice differences like these if they are looking for them.
Sometimes cybercriminals don't spoof the entire email address, but rather just the display name. For example, in some email platforms, like Outlook, a person's display name is shown in the 'From' header before the email address. And some email clients hide the email address altogether to make the interface less cluttered. Unfortunately, this allows attackers to only manipulate the display name, leaving their actual address in the 'From' header while remaining confident that it won't be seen.
How to Protect Yourself Against Email Spoofing
The Technical Way
Check whether the email passed a Sender Policy Framework (SPF) check. SPF, DMARC, and DKIM are authentication checks that happen in the background when you receive an email. Not all email domains have these protocols activated, but all well-established and professional brands will. How you check whether the SPF passed or failed will vary depending on your email client, so you'll want to Google how to do it on the one you use.
Don't Click on Links
If you receive an email asking you to log in to an account or authenticate your details, don't click on the link within the email. Instead, navigate to the website yourself.
Check To See if the Email Has Been Associated With a Phishing Attack
If in doubt, copy and paste the email body text into Google and see if anyone else has reported it as suspicious. Taking this simple step can save you a lot of trouble.