What Is A Botnet?

A botnet is a piece of malware that can infect any computer to carry out commands.
These commands are under the direct control of the attacker, and this can cause a lot of damage. Today, this type of malware is one of the biggest threats to security systems.
This is a classic example of using good technologies for bad intentions.
Botnets are called “the workhorses of the internet”.
They are a network of connected computers that keep websites functional.
Their features are useful and beneficial for maintaining smoothly running websites and delivering positive user experience.
Yet there is also a dark side - illegal and malicious botnets.
These are becoming a part of the cultural discussions for cybersecurity, as they can infiltrate any internet-connected device from DVR players to corporate mainframes.
The use of this technology is becoming a growing business for cybercriminals and this trend will continue as more computers are infected with mining software.
They are dangerous for corporations and consumers also as they deploy malware, initiate the attack on the websites, personal information is stolen, and also defraud advertisers.
Any computer can be a part of a botnet and cybercriminals can establish a large network of “zombie machines”, as well as selling their access to other cybercriminals.
Illegal And Malicious Botnets
The illegal variety of this technology gains access to a machine with the help of malicious coding.
The machine can be directly hacked in some cases.
In some other cases, it is accessed by a “spider” – a program that crawls through the internet in search of gaps in security that can be exploited.
The ultimate goal of this malicious goal can be financial gain, malware propagation, or just to generally disrupt the internet.
How Do They Work?
This type of malware can add a computer directly to their web by a drive-by-download, or by tricking a user into installing a Trojan horse on their computer.
As software gets downloaded, the malware gets connected to its master computer and shares all information.
Through this process, the computer or device is completely under the control of the person who created that particular malware.
This strategy is typically used to infect the system of the user itself.
Once the computer is in control, the machine can be used for other malicious activities such as:
- Using the machine's power to shut down websites by assisting distributed denial-of-service (DDoS) attacks.
- Sending spam emails to millions of internet users.
- Generating fake internet traffic for financial profit on a third-party website.
- Replacing web browser banner ads specifically targeting the user.
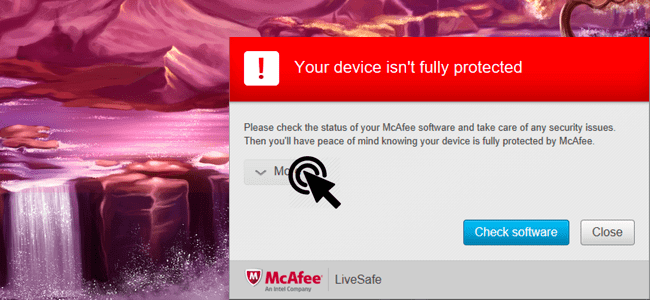
- Creating pop-up ads on the user’s browser, and to remove these pop-up ads the user has to pay through an anti-spyware package.
How You Can Protect Yourself?
Prevention of this type of infection involves a comprehensive strategy that should include safe internet surfing habits as well as antivirus protection.
Taking some simple precautions can remove malware that has already been installed and also prevents it from happening again.
Here are some ways to keep botnets at a bay:
- Keep your operating system updated. One should set their OS to update automatically and make sure that they are running the latest version.
- Email attachments are the main source of any type of virus to enter a system. Never open an attachment from an unknown source. Bots generally use contact lists to compose and send spam emails that infect other systems.
- Avoid downloading from P2P and file-sharing networks. Any type of downloads should be scanned and safer alternatives should be used for transferring files.
- Never click on suspicious links. When browsing, use a firewall. If you have any doubt about a link, you can check it with Norton Safe Web.
- Make sure to regularly update your device’s OS. Security patches are released frequently, and updating the OS regularly will ensure that no malware infects your device and data.
Bottom Line
This malware type generally searches for vulnerable devices on the internet.
However, it is very difficult to detect an attack on an individual level because devices continue to function normally even when infected.